GNU/Linux: Error message 'error opening serial port', 'avrdude: ser_open(): can`t open device <port>', 'permission denied'
What to do if you can't get access to the serial port/USB under GNU/Linux?
If the access rights to device files (serial ports, USB) are not set appropriately under GNU/Linux, the user can neither program a microcontroller nor use the mining software 'AVR_Miner.py'.
If you want to program an Arduino UNO with the Arduino IDE for the first time, you will almost always run into the problem under GNU/Linux that the IDE does not have access to the serial port (i.e. USB) and thus cannot find the microcontroller. The solution: Correct group membership (and not release device files for all/everyone as often described!).
Access to serial USB
The Arduino IDE works "out of the box" - with one exception: you cannot write to the serial ports and thus cannot access USB devices. This is a sensible security setting in Unix systems like Linux or the BSDs. Linux follows (at least partially) the philosophy of Unix: "Everything is a file", which is why USB devices are also mapped as files in the directory tree. If you plug an Arduino UNO into a USB port, it appears as a file in the /dev directory:
mipl@t5500:~$ ls -l /dev/ttyACM* /dev/ttyUSB* crw-rw---- 1 root dialout 188, 0 14. Feb 09:03 /dev/ttyACM0
What does the information in the second line mean?
- crw-rw---- Access rights for UGO (User "rw", Group "rw", Others "--")
- root dialout The file/device belongs to root and the group dialout.
- 14 Feb 09:03 At this point the file was created (Arduino plugged in).
- /dev/ttyACM0 The name of the file through which the Arduino UNO can be accessed.
By the way: Original Arduino UNO/Nano log on to the system as /dev/ttyACMx, clones on the other hand as /dev/ttyUSBx.
PermissionError: [Errno 13] Permission denied: 'dev/ttyACM0'
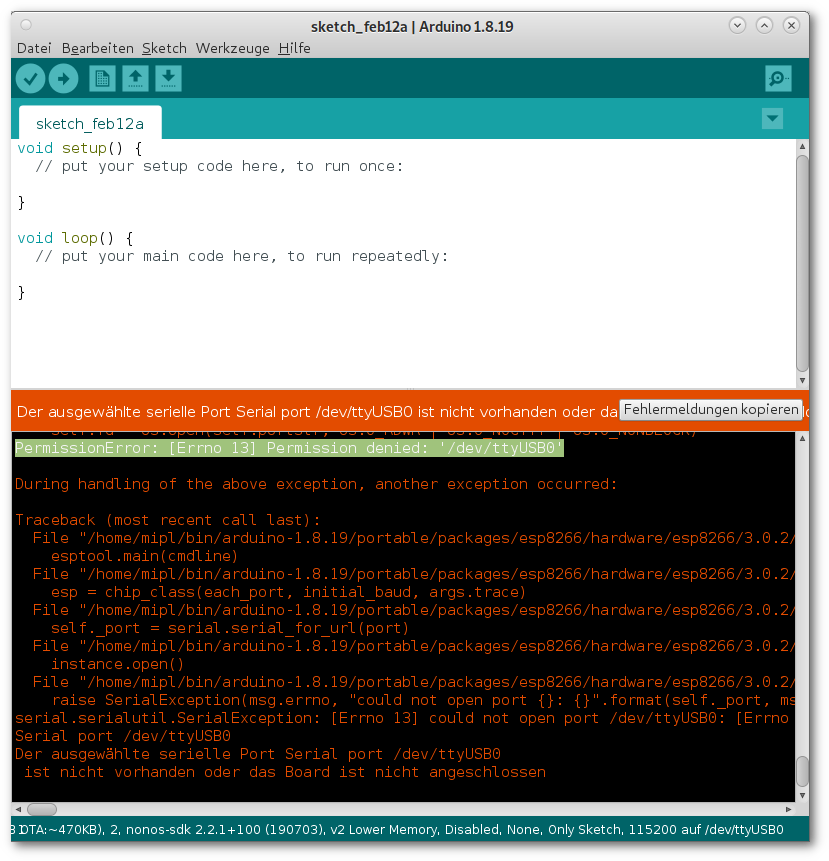
If there is an error message when accessing the serial port (USB port /dev/ttyACM0 on original Arduino UNO, /dev/ttyUSB0 on Clones), the user lacks the rights to access this device/file. Under no circumstances should you, as is often stated, make the device file belong to the user (chown ttyACM mipl:mipl) or even release the access rights for everything and everyone (chmod 777 ttyACM0). This is extremely insecure and stupid. Instead, the user must join the "dialout" group (for modem and thus serial/USB access). This must be done with root privileges and looks like this:
sudo usermod -a -G dialout mipl
This adds "mipl" to the group dialout. With "-a" the specified group is added (without "-a" "dialout" would then be the only group). After "-G" all groups (several are separated by commas) are listed which the user is to join.
If you now enter the id command again, you will see that the user has been added to the group dialout. As a user, however, this group membership is not yet visible. Annoyingly, you have to log in again or restart the system for the change to take effect for the current session.
In the standard installation, you are not a member of the dialout group. This group is allowed to access serial interfaces (dialout = to dial out, originates from times of data transmission via modem).
After a restart, calling id shows that you are not root (you should never work as root, no matter under which operating system), but that you belong to the group dialout:
mipl@t5500:~$ id uid=1000(mipl) gid=1000(mipl) Gruppen=1000(mipl),24(cdrom),25(floppy), 29(audio),30(dip),44(video), 46(plugdev),102(netdev)
Now you can program microcontrollers via the Arduino IDE (or avrdude) and control the Arduino UNO via
python3 AVR_Miner.py
to mine Duinocoin (DUCO).